PearlCTF 2024: The-3-Fragmenteers [Forensics] WriteUp
This was my second shot at a CTF competition and I’m proud of solving a challenge outside my usual comfort zone. My team was astralis — me (prix) and my mate Darsh Patel (trench).
The Challenge
The download was a .7z archive containing a memory dump: dump_3.raw.
Getting Started with Volatility3
Initial image analysis:
python3 vol.py -f dump_3.raw windows.info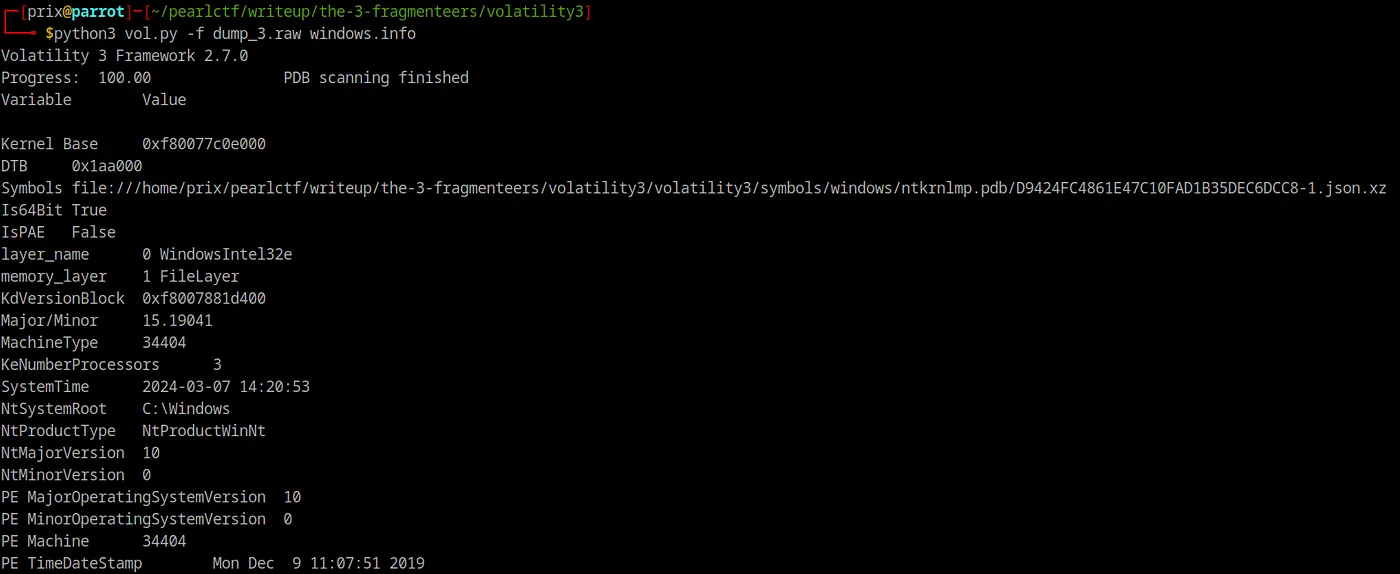
Confirmed it was a Windows memory image.
Scanning for Files
python3 vol.py -f dump_3.raw windows.filescan > filescan.txt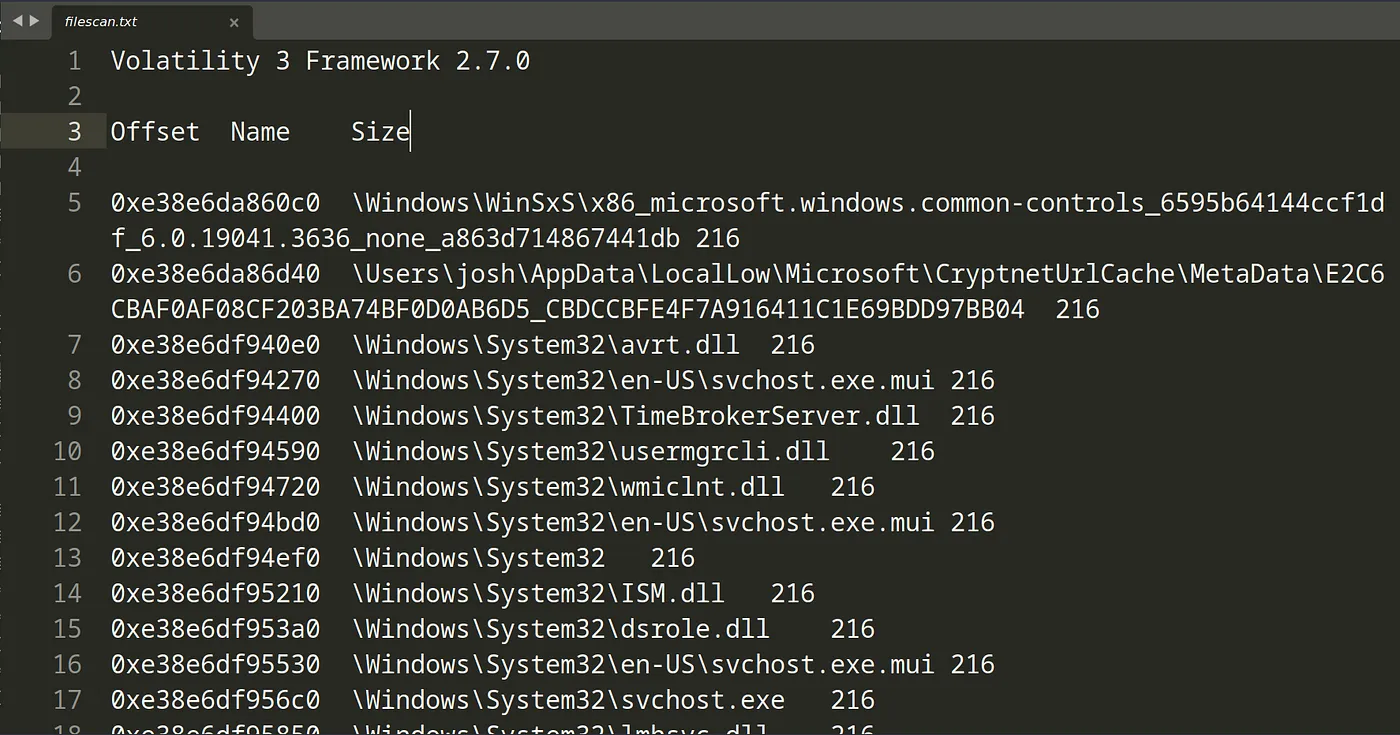
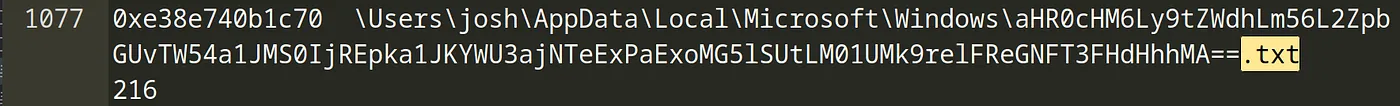
Searched through the output for .txt files and found three suspiciously named files:
Extracting the Files
Dumped each file by its virtual address:
python3 vol.py -f dump_3.raw windows.dumpfiles --virtaddr 0xe38e74c110f0python3 vol.py -f dump_3.raw windows.dumpfiles --virtaddr 0xe38e7500d270python3 vol.py -f dump_3.raw windows.dumpfiles --virtaddr 0xe38e740b1c70Following the Trail
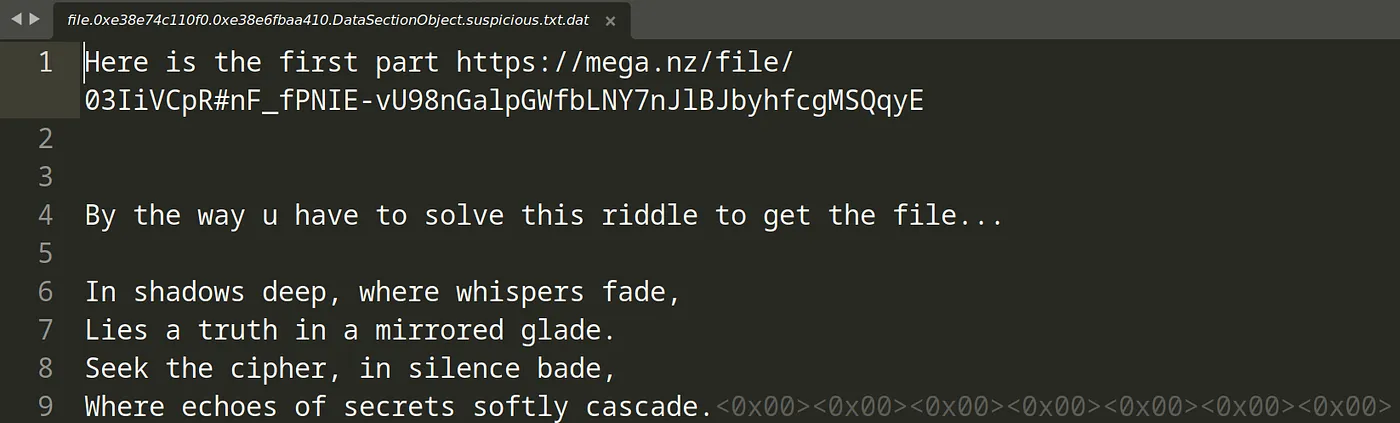
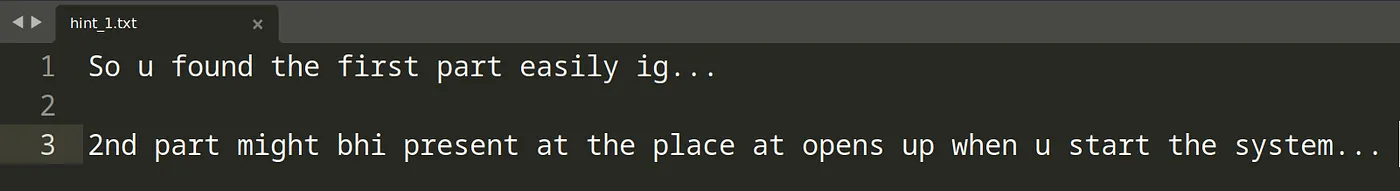
File 1 (suspicious.txt): Contained a Mega.nz link and a riddle. The password to the hosted .rar was reflection. Inside: hint1.txt and xaa.unknown.
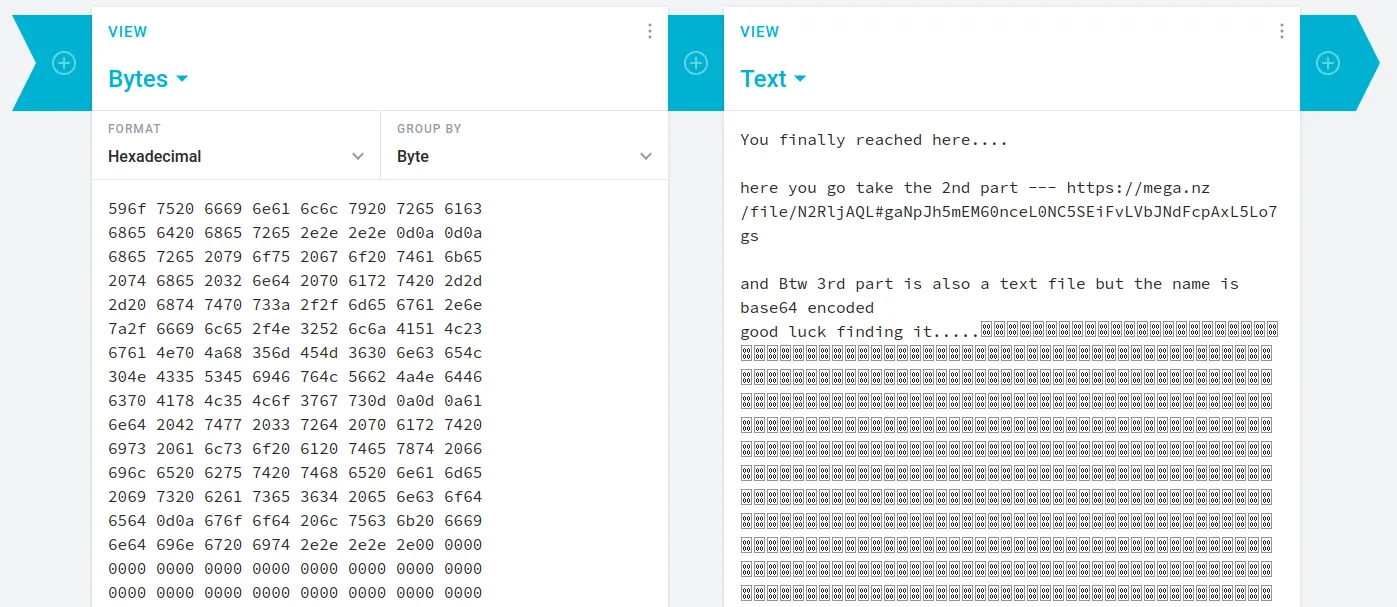
File 2: Contained hex data. Decoded via Cryptii — revealed another Mega.nz link with xab.unknown and a hint that the 3rd file’s name is base64 encoded.
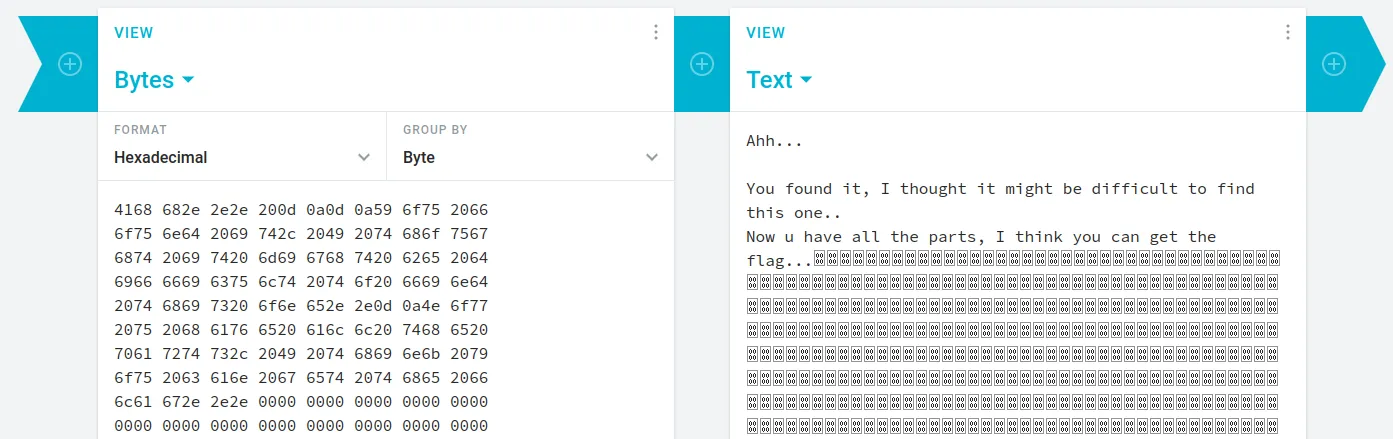
File 3: Decoded the base64 filename to get the final Mega.nz link with xac.unknown.
Reassembling the Fragments
Merged the three files — turned out to be a split PDF:
cat xaa.unknown xab.unknown xac.unknown > newfilefile newfile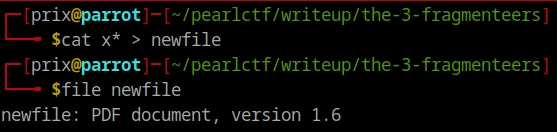
Opened the PDF and found the flag inside:
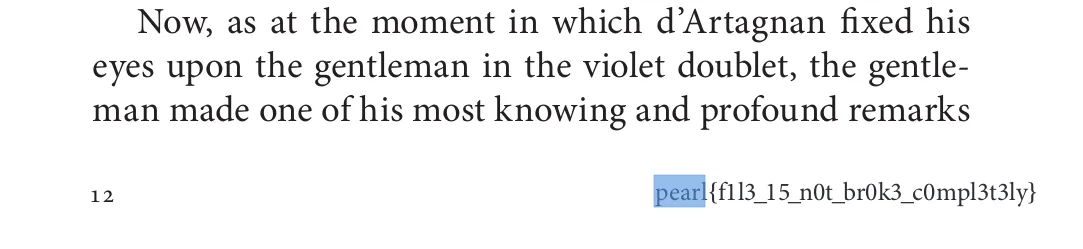
FLAG: pearl{f1l3_15_n0t_br0k3_c0mpl3t3ly}
← Back to blog