BSides Galway 2026 CTF: Intro [Web] WriteUp
Almost a month late, but better late than never! BSides Galway 2026 had a really fun beginner-friendly web challenge called Intro that I thought was worth documenting. It’s split into three flags and walks you through some core web fundamentals in a pretty clever way.
The Challenge
Three flags. Let’s get into it.
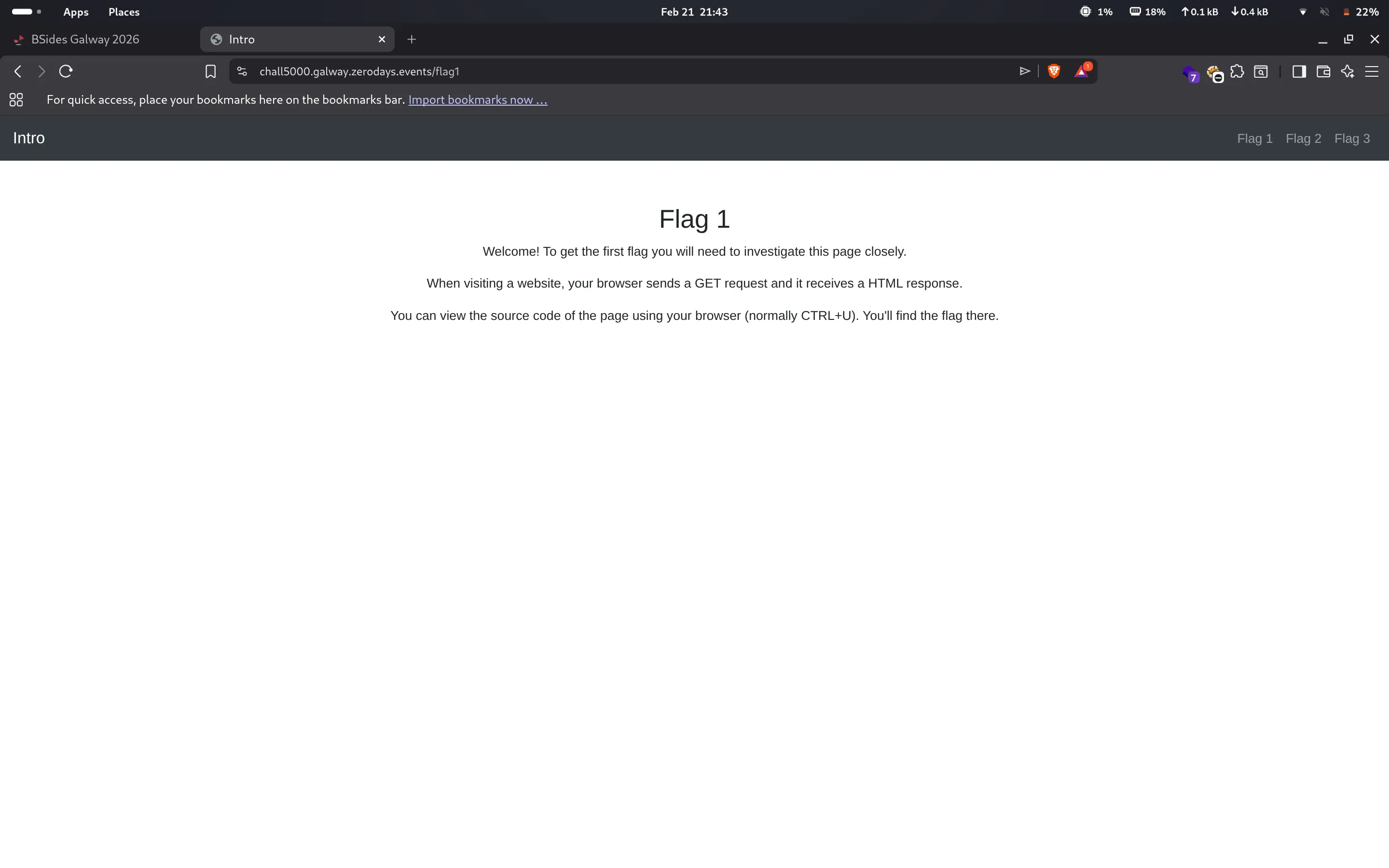
Flag 1: View Source
The first flag hints that you need to “investigate the page closely.” When visiting a website your browser sends a GET request and receives an HTML response - and you can view that raw HTML with Ctrl+U.
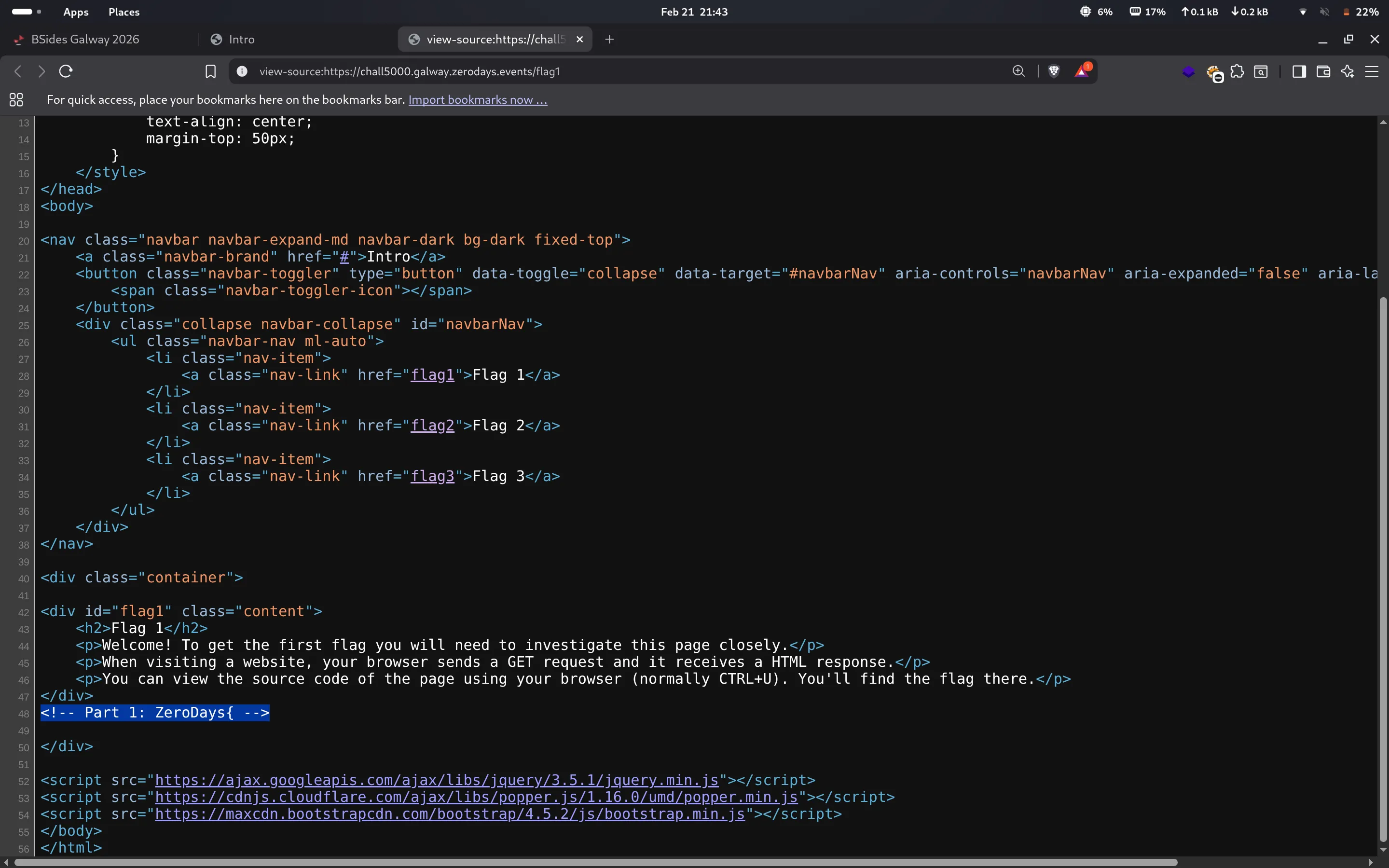
Sure enough, going to the page source revealed a hidden HTML comment with the first part of the flag sitting right there.
Flag 1: ZeroDays{... (Part 1 hidden in the HTML comment)
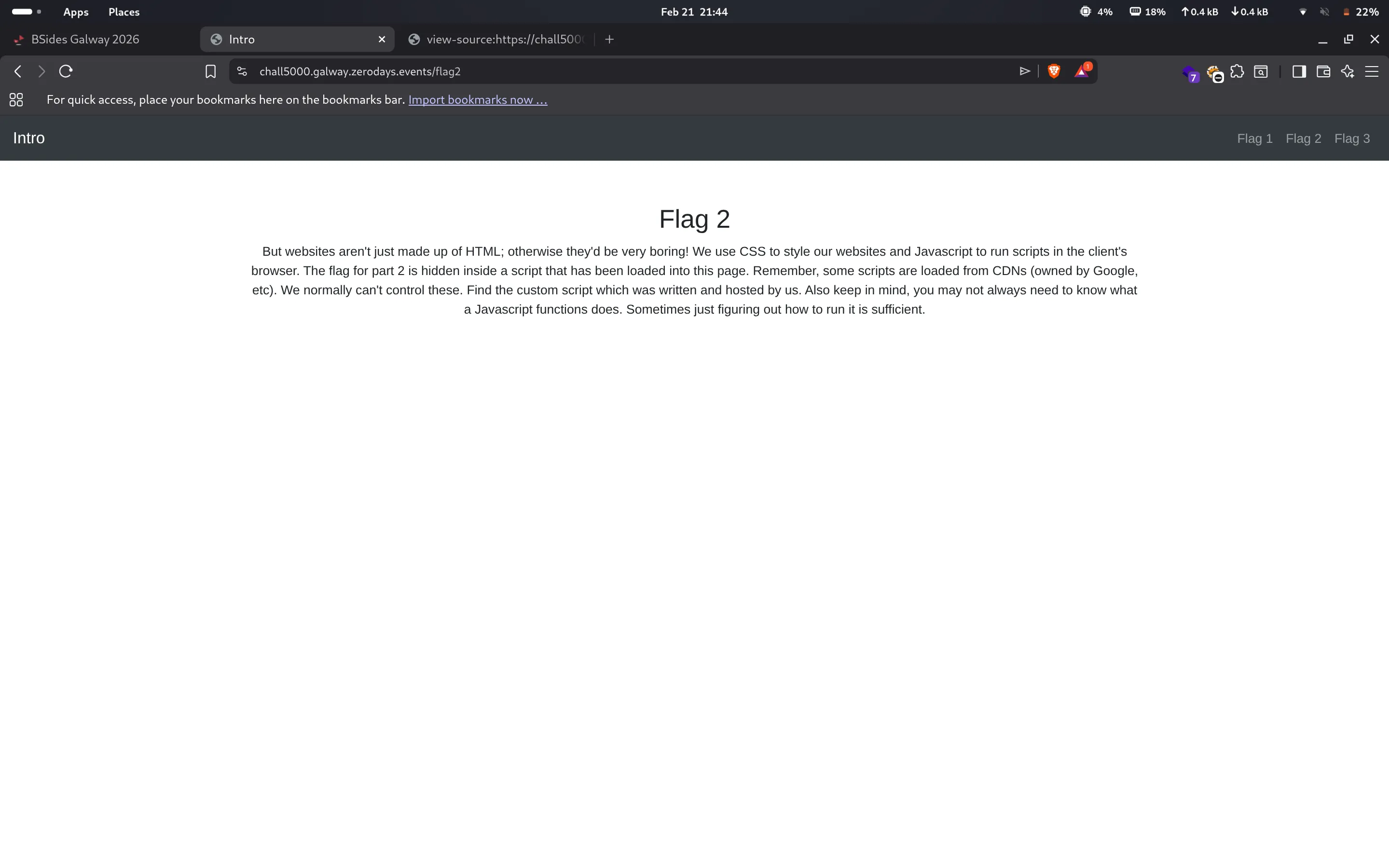
Flag 2: Deobfuscating JSFuck
Flag 2 is hidden inside a script loaded into the page. The hint tells you to find the custom script hosted by the challenge authors - so that gives me a clear indication to ignore scripts like jQuery or Bootstrap.
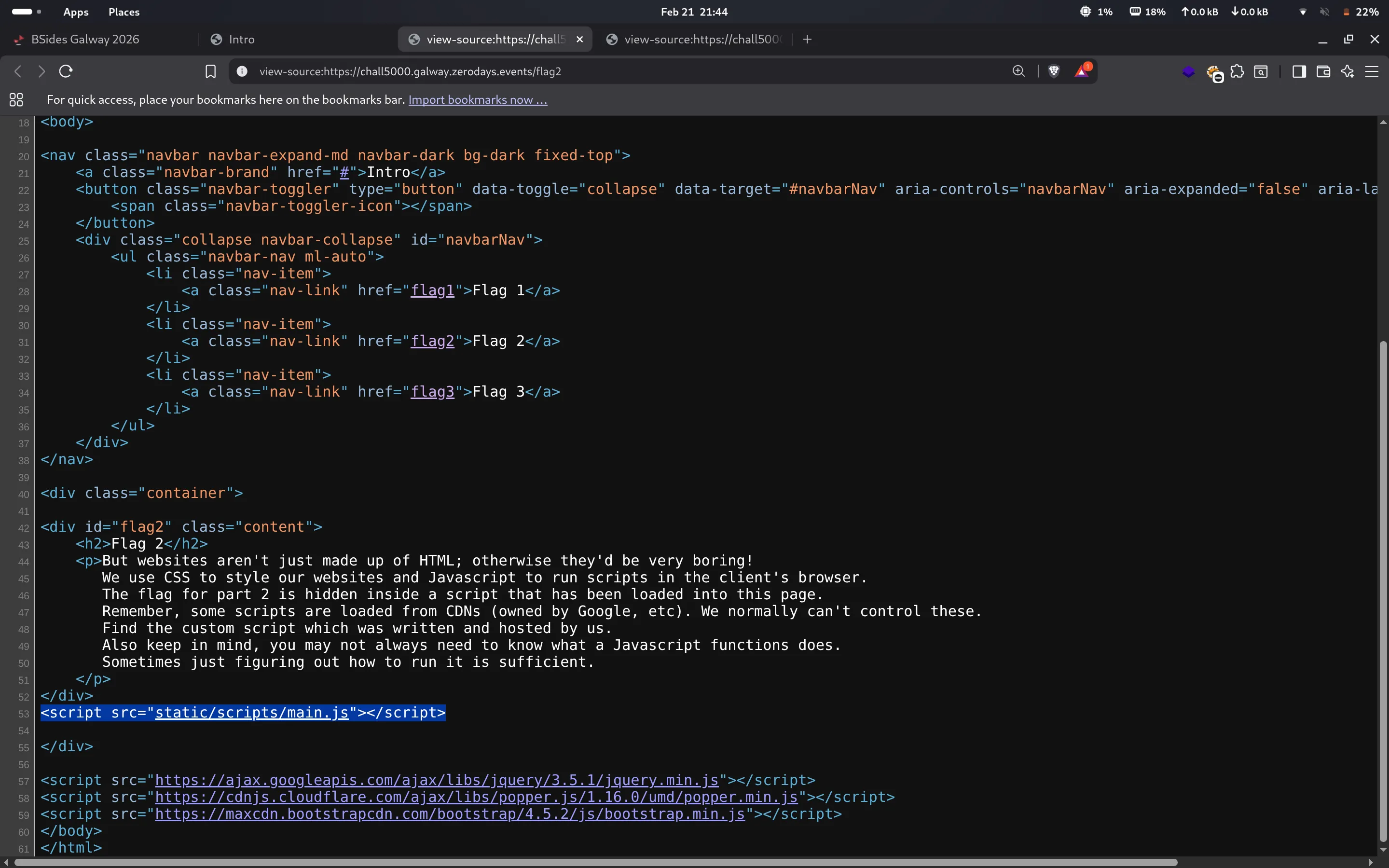
Navigating to the custom script at static/scripts/main.js revealed an entire page of JSFuck a JavaScript obfuscation technique that encodes any code using only [, ], (, ), !, and +.
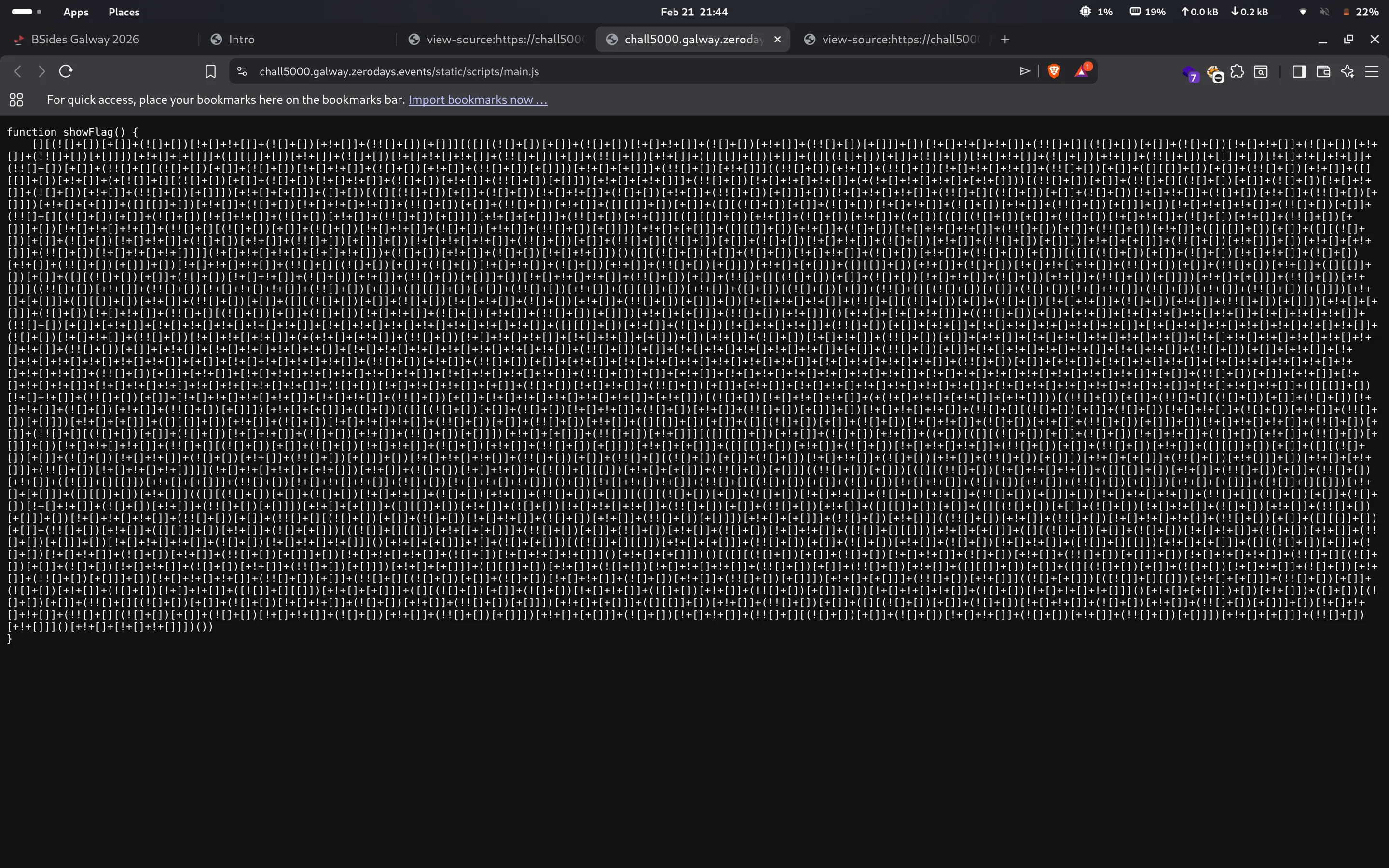
Threw it into a JSFuck decoder and it decoded to a simple console.log containing the second part of the flag.
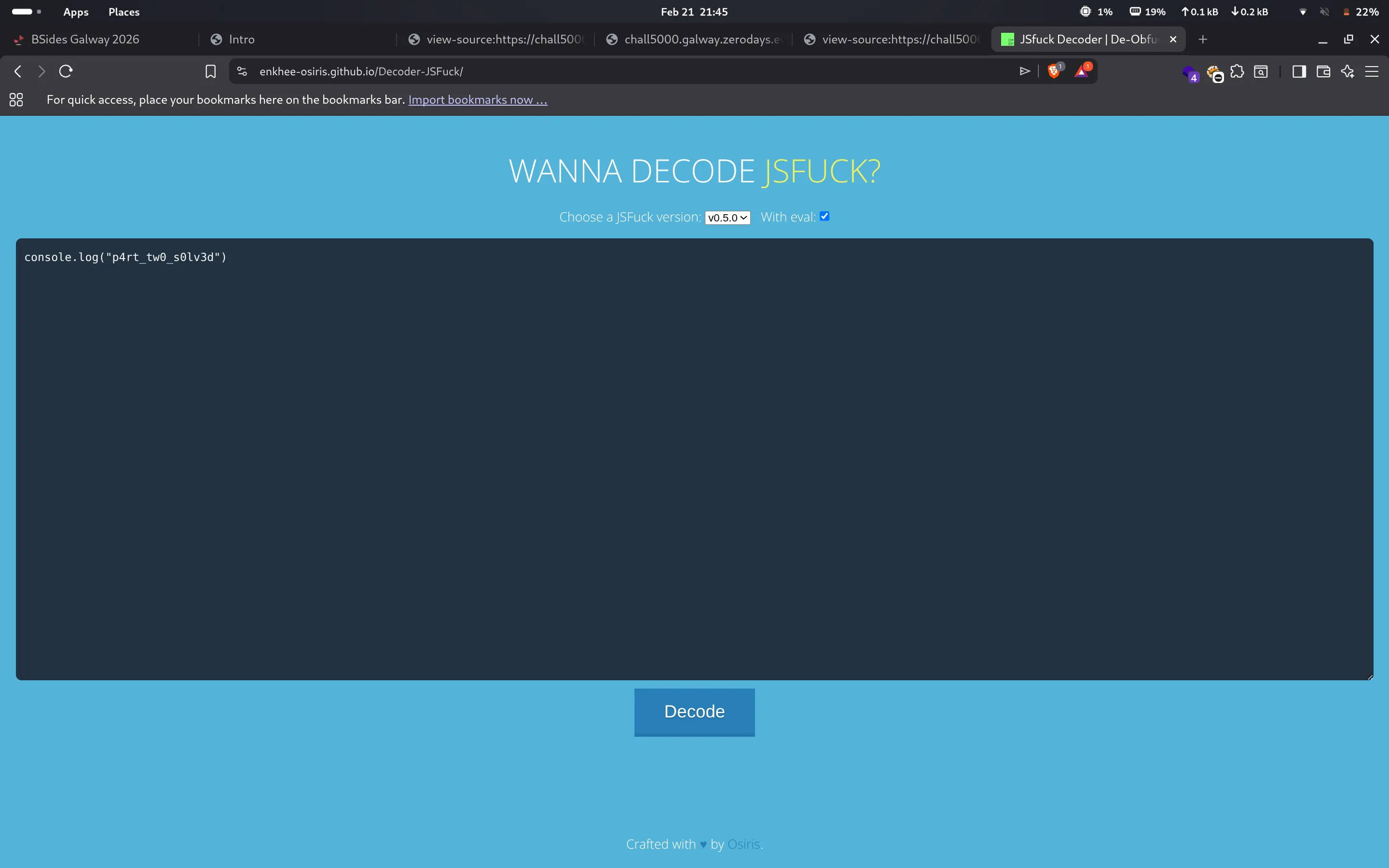
Flag 2: p4rt_tw0_s0lv3d
Flag 3: Crafted HTTP Request
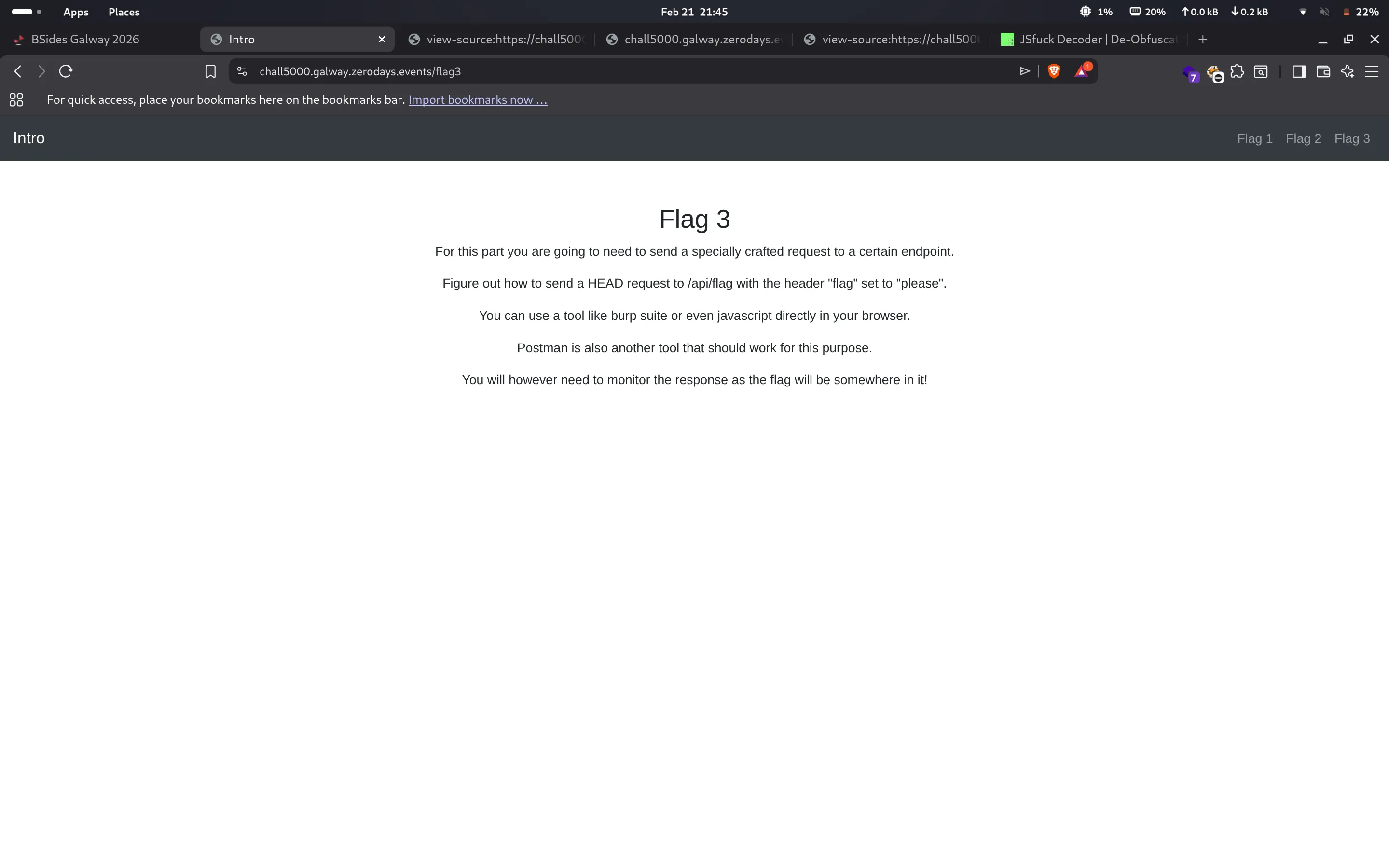
Flag 3 is where it gets a bit more technical. The challenge asks you to send a HEAD request to /api/flag with a custom header flag: please and monitor the response headers for the flag.
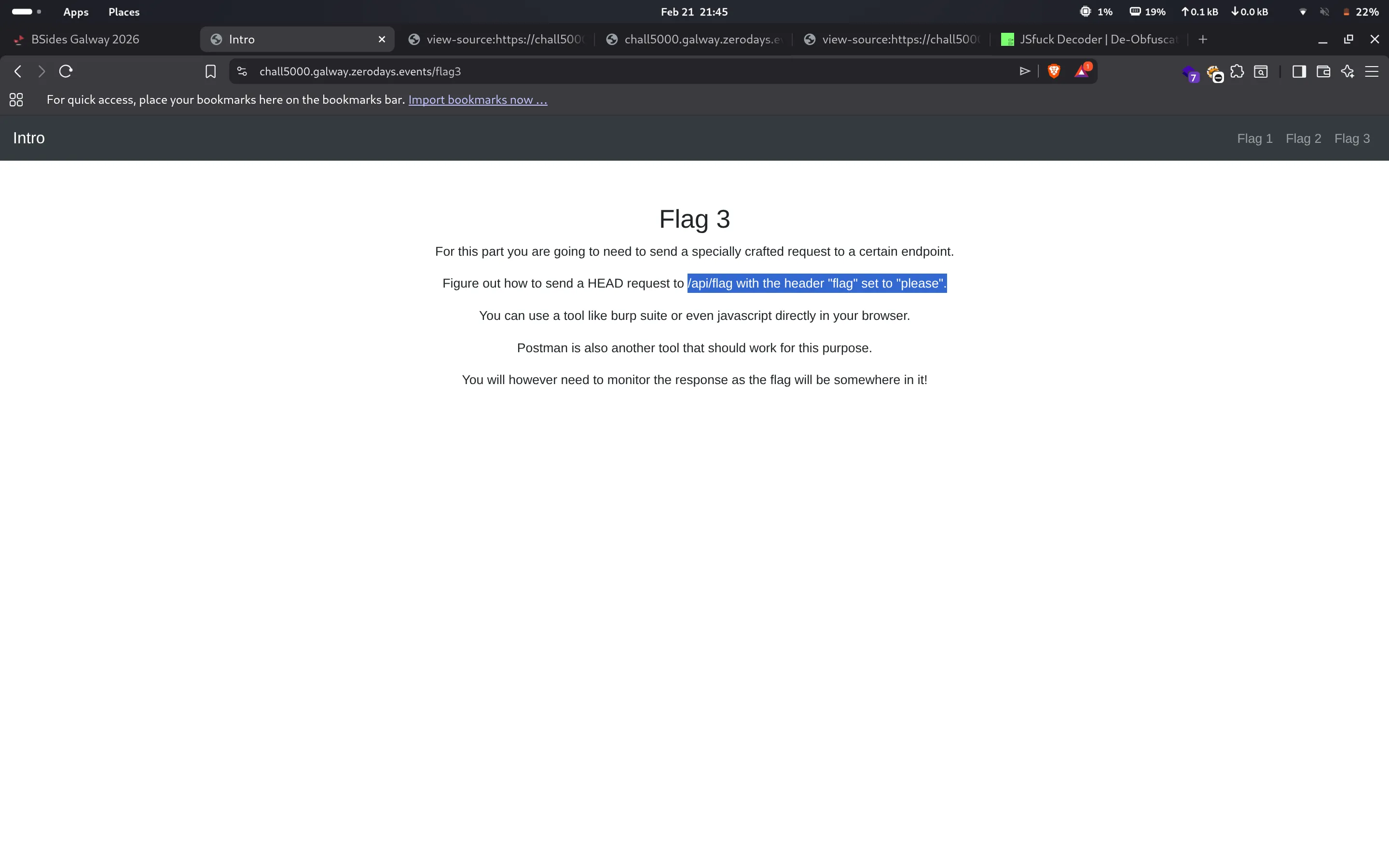
Tools like Burp Suite or Postman would work well, However, I went with a simple curl command:
curl -I -H "flag: please" https://chall5000.galway.zerodays.events/api/flagThe -I flag sends a HEAD request, and -H adds the custom header. The response came back with the flag tucked away in the response headers.
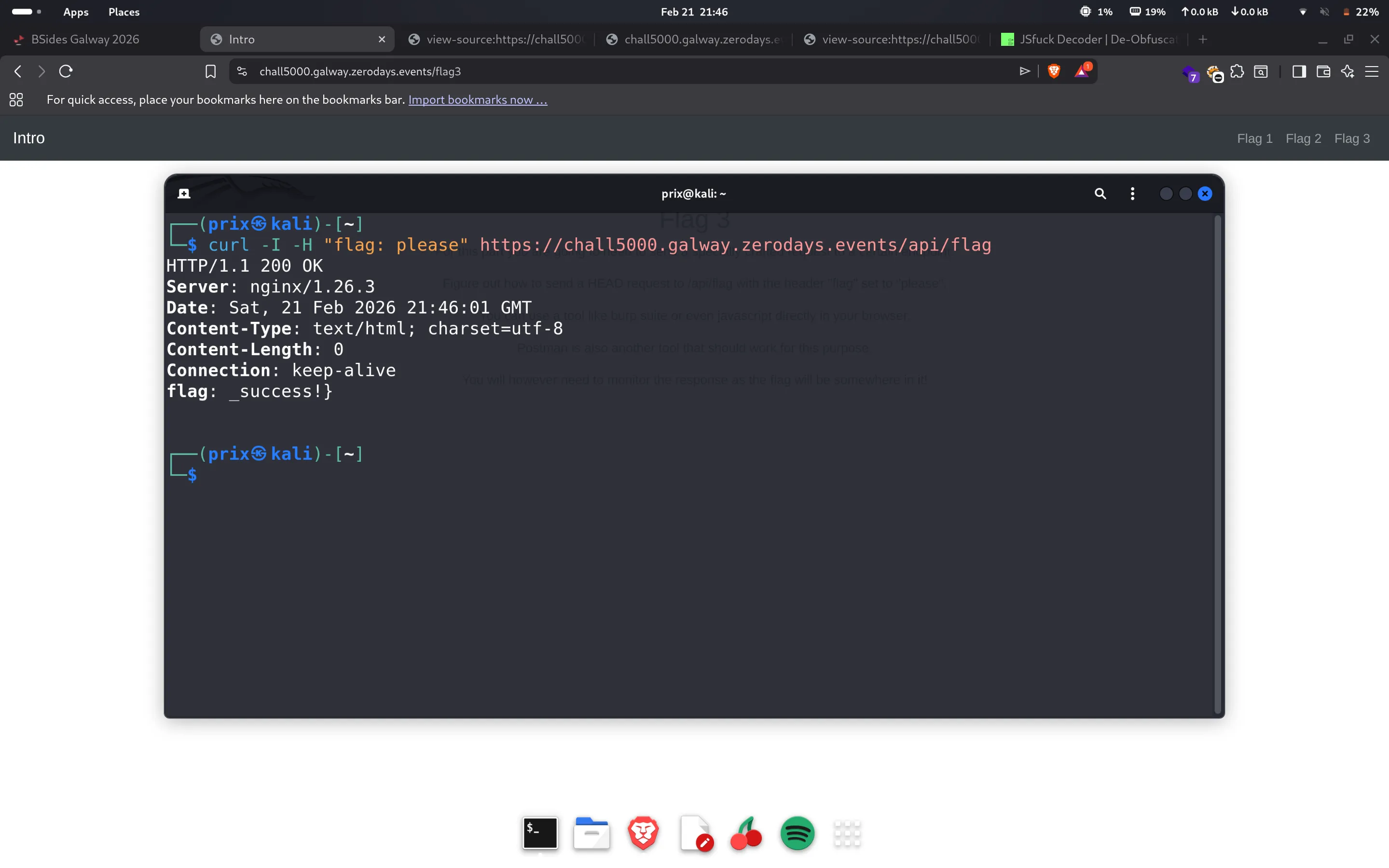
Flag 3: _success!}
Overall a solid beginner friendly web challenge that covers various aspects. Thanks to the ZeroDays team for this challenge! Much appreciated.
← Back to blog